
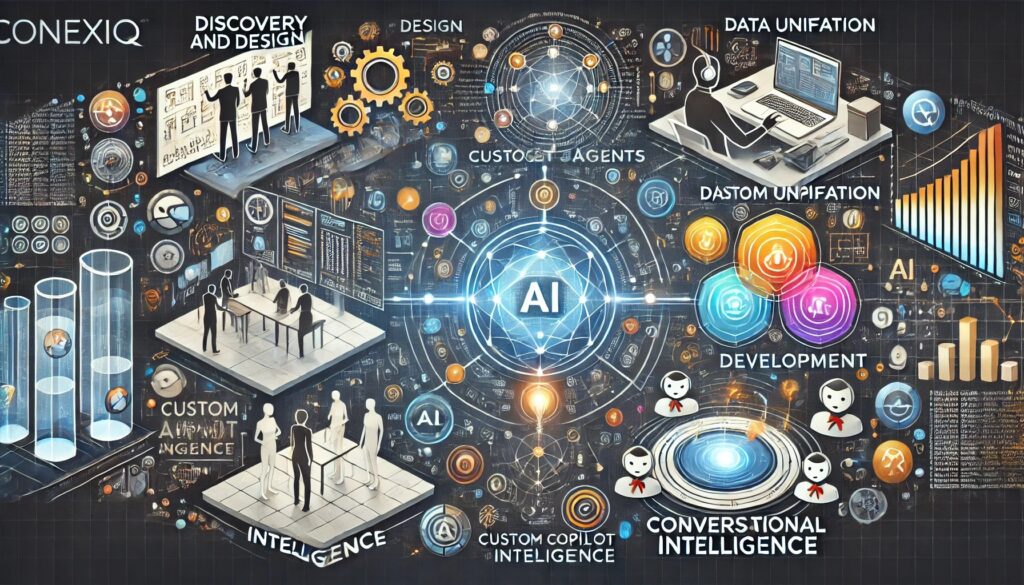
Unified Solutions from Conexiq: Intelligent Agents Redefining Work
Unified by Design, Powered by Intelligence
The future of business isn’t about managing more tools—it’s about unifying workflows into a seamless, intelligent experience. Conexiq’s Unified Solutions are powered by intelligent agents that act as custom copilots, transforming how businesses interact with their data, processes, and teams.
Unified, Intelligent, Seamless
Data Unification: By connecting to your existing data sources and systems, we create a unified ecosystem that powers smarter workflows.
Agent Development: Leveraging declarative frameworks or building custom engines, we craft agents that seamlessly integrate with your processes.
Conversational Intelligence: We enhance agents with conversational AI, enabling intuitive and natural user interactions.
Deployment and Optimization: Our solutions are deployed with scalability in mind, ensuring they grow with your business. Continuous feedback loops allow for iterative improvements.
The Conexiq Advantage
Unified Workflows: Say goodbye to disconnected tools and siloed data.
Proactive Solutions: Intelligent agents anticipate needs and streamline actions.
Customizable for Your Business: From simple automations to complex processes, our agents adapt to your unique requirements.
Conversational Interfaces: Empower users to interact with data in natural language, making every interaction faster and easier.
Future-Proof Technology: Built to evolve with AI advancements and changing business landscapes.

Unify, Simplify, and Revolutionize Your Business with Conexiq.
The Future of Work is Unified
At Conexiq, we don’t just build solutions—we redefine how work gets done. Our intelligent agents/custom copilots, and unified systems ensure your business isn’t just keeping up with the future—it’s leading it.
Declarative Agents: Simplicity Meets Power
Our declarative agents are designed to deliver no-code and low-code solutions, empowering businesses to build workflows and automations without the need for complex programming.
- For Everyone: Declarative agents make it easy for anyone in your organization to configure processes.
- Rapid Implementation: Build, deploy, and iterate quickly with intuitive drag-and-drop interfaces.
- Business Ready: Automate common tasks like document management, approvals, or customer interactions effortlessly.
Custom Engine Agents: Tailored to Your Needs
When businesses need more than out-of-the-box solutions, our custom engine agents step in to create highly specialized capabilities.
- Industry-Specific Solutions: Whether it’s GRC tools, enterprise automation, or advanced analytics, our custom agents are built to meet unique requirements.
- AI-Enhanced Logic: Harness advanced algorithms to manage complex workflows and derive insights from your data.
- Scalable and Secure: Built for growth, our agents scale with your business while maintaining the highest security standards.
Unified Data Sources with Conversational AI
At Conexiq, we understand that data is the lifeblood of any organization—but accessing and using it shouldn’t be a chore. Our solutions unify data from all your sources—CRMs, ERPs, SharePoint, APIs, and more—and make it accessible through conversational AI.
- Seamless Integration: Connect disparate systems into a unified data ecosystem, enabling smooth interactions.
- Conversational Access: Use natural language to query, manage, and analyze data across platforms.
- Example: “What’s the current status of Project X?” or “Generate a sales report for the last quarter.”
- Real-Time Insights: Get immediate, actionable insights without digging through multiple apps or systems.

